Back in 2016, I wrote about the U.S. Government losing control of high-level security software (AKA, “hacking tools”). Now, the New York Times is reporting that the City of Baltimore has been hacked.
You see, years ago, the NSA (allegedly) found a bug in Microsoft Windows, then developed an application that used the bug to make a computer running that version of Windows run whatever program they wanted. The code worked so well that they didn’t tell Microsoft about it. In other words, not only did the NSA have a hacking tool, but the tool used a then-unknown bug in Windows (so, Microsoft, unaware of the bug, was perhaps not even working on a fix for the bug). So called “zero day” exploits can be extremely valuable, extremely powerful, and extremely hard to detect.
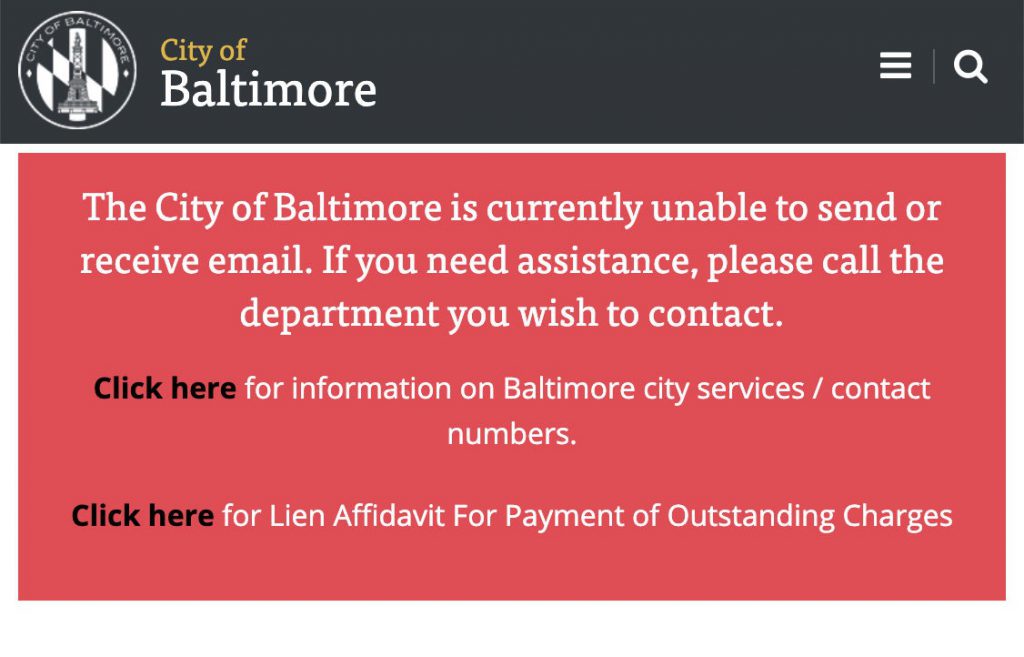
The problem is, as I wrote about back in 2016, the NSA’s set of hacking tools were unintentionally released into the wild. Now, those same tools are being used against the City of Baltimore, which is now the subject of a ransomware attack. The hackers have “locked” Baltimore’s computers and are asking for $100,000 in Bitcon to unlock them.
What does this mean for you? Assuming you are not in impacted by the Baltimore attack, you can take this opportunity to be more vigilant. More specifically, you could take the following steps:
- You, or your IT staff, can apply security fixes as they become available. While this should be part of your standard operating procedure, now is as good a time as any to start doing this.
- You can contact your cloud-based and software-as-a-service vendors to make sure that they are aware of the issues and are applying fixes as necessary.
- You can review your contracts with your vendors. One of the things that it’s possible to negotiate (and you may have negotiated) the level of care your vendor must take with your data. You might also consult with your lawyer to help review your contracts (and perhaps negotiate new ones).
- Another thing you can negotiate is the response to a data breach. Because security breach notification laws can impose obligations for certain kinds of security breaches, many companies negotiate who must comply with these obligations in their contracts with vendors who handle data (e.g., where software-as-a-service handles nonpublic personal information). You might also consult with your lawyer about your contracts and negotiation of new ones.
- You can look into obtaining insurance coverage for security breaches. And, you might also consult with your lawyer to give you advice about whether your current insurance policy, or any new policy you might consider, covers you for these risks.
- You can stop and reevaluate your software systems to make them harder to exploit. Many of these tools are designed to break into computer networks and extract information. Encryption of data, whether at rest or in motion), is a best practice; and, encryption that is rigorously tested and well-implemented can make it significantly harder for hackers to reach sensitive data.
- You can implement policies to avoid collecting or holding onto sensitive information you don’t need. If you don’t have it, they can’t steal it from you.
- You can train your employees to avoid inappropriate use of email. Don’t you think Sony wishes they had been more careful with their emails? Dance Like No One is Watching; Email Like It May One Day Be Read Aloud in a Deposition.
Leave a Reply